Cybersecurity
Research Background
-
On connected cars and Automated Driving for Universal Service (adus), data related to vehicles, human factors, infrastructures and others, which are collected through network outside the vehicle then sent to control or information devices, are utilized to control vehicles or for other purposes. This circumstance makes it possible not only to create unprecedented services, but also to cause cybersecurity issues never happened before on traditional vehicles. As examples, new types of cyberattack methods against vehicles have been reported one after another in recent years at international conferences such as BlackHat, which means that it is necessary to take actions against these threats. The countermeasures against cybersecurity attacks on vehicles are also demanded from a legal perspective as UNECE WP29 released UN-R155.
Under this changing cybersecurity environment and legal requirements as result of increased use of automated vehicles, our project is working on 2 themes: a) Creation of IDS#1 validation methods and these guidelines and b)Research and study for threat data and cyber incident initial response support for connected cars, to realize continuous safety and security on vehicles after delivery.
The former as a) is for validation methods of IDS as one of effective approaches to detect malicious third-party attacks, and the latter as b) is for a system to detect and share ,on early stage, cyber threats which may newly arise after delivery.#1 IDS:Intrusion Detection System
-
Project Outline
-
Theme a:Creation of IDS validation methods and these guidelines
[Summary]
Baselines for validation methods and validation criteria of in-vehicle IDS will be derived then utilized to create guidelines which will be handed over to a relevant industry association, together with which we will work to apply the guidelines into business and operate them in automotive industry. The guidelines include validation methods that can be mainly applied to development with ready-made parts. Our objectives are not only to give broader options for IDS development, but also to contribute to accelerate the development process of OEM and suppliers as our target readers of the guidelines, who are struggling with time-consuming first stage of development.
[Goal]
The final goal is determined as to transfer the IDS validation methods guidelines operation to a relevant industry association.
- Element analysis for basic features of each types of IDS will be followed by defining requirements based on already-known and specific past cases, then by tests with testbeds and whole vehicle, or with whole vehicle test bench. Based on the results of the tests, will be created guidelines before the end of FY2021.
- Therefore, it is necessary to make outline of the guidelines by the end of FY2020 after collecting data necessary for the tests, such as case studies of recent cyber-attacks, research on IDS and others, as well as after defining details of the test.
- Based on the FY2019 activities, interviews and discussions will be proceeded as necessary with stakeholders in related industries for both of business implementation and smooth transition of the guidelines operation.
Theme b:Research and study for threat data and cyber incident initial response support for connected cars
[Summary]
We will study methods to collect and store data related to threats for immediate response to cyberattacks that may newly arise after delivery. While creating operational tests plan to watch attacks through honeypot for proactive collection of threat data, basic requirements of system to support first response will be defined as well. The achievements through these activities will be handed over to a relevant industry association aiming to accelerate data sharing for cooperative research area as well as to raise level of cyber incident response capability in whole of the related industries.
[Goal]
The final goal is to transfer operations of the system basic requirements that can support cyber incident first response to a relevant industry association before the end of FY2022.
- Methods to collect and store threat data as well as basic requirement to support first response using the methods will be prepared before the end of FY2021, based on assumption that data sharing among relevant industries with “ data sharing system” would have effectivity to help first response against incidents.
- The operation of the system applied into business will be completely transferred before the end of FY2022 to a relevant industry association, accompanied by defined basic requirements for the whole of the system to operate the above mentioned factors, as our final goal.
-
Project Members
-
Theme Leader
Yasumasa Hirai Group Manager, E/E Architecture Development Div., Toyota Motor Corporation
Participating bodies
PwC Consulting LLC
Yokohama National University
-
International Cooperation
-
- Overview of German-Japanese research collaboration
We have 4 active projects for the R&D on the connected (automated) car security, which are led by BMBF#2 , and additional collaboration with “SecForCARs” since July 2021.
※1:The Federal Ministry of Education and Research (Bundesministerium fur Bildung und Forschung) -
Themes for Japanese-German collaboration activities
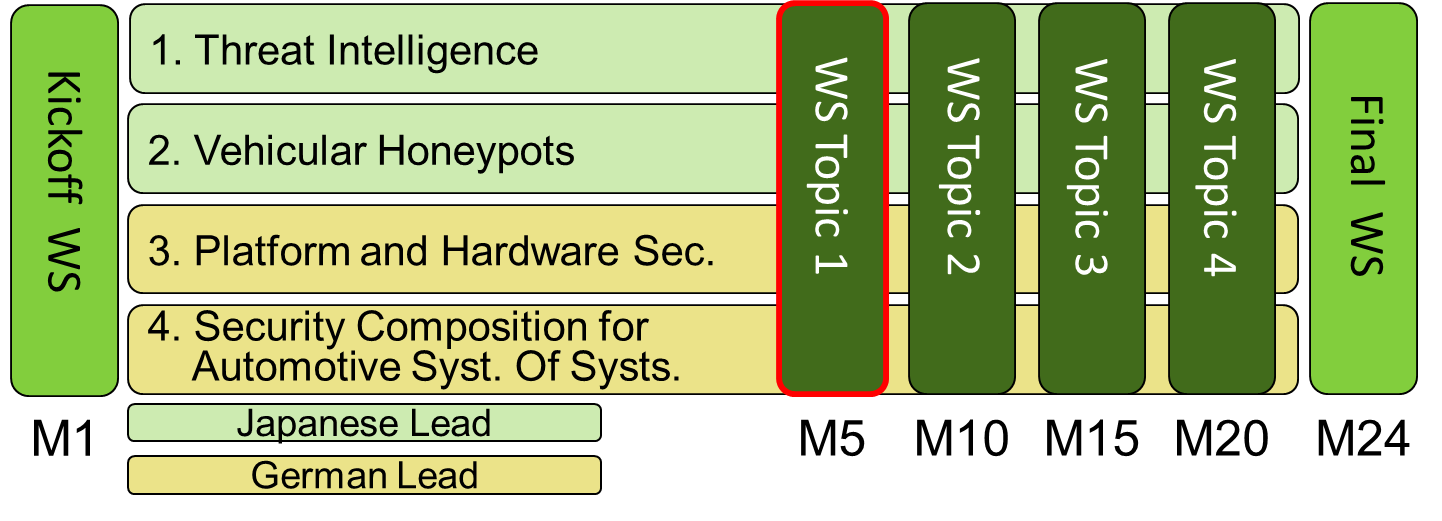
- Threat Intelligence (Japanese Lead)
- Vehicular Honeypots (Japanese Lead)
- Platform and Hardware Security (German Lead)
- Security Composition for Automotive System Of Systems (German Lead)
- Activities status of Japanese-German collaboration
We have, in total, 5 workshops to share and discuss activities of both countries, Japan and Germany, linked to Cybersecurity. The occasions are utilized as input to future activities of each. The 3 workshops has been already held for the sharing and the discussion of activities in Japan and Germany related to: studies and tests for Threat Intelligence and Vehicular Honeypots from Japan side as SIP-adus research themes, and from Germany side, Platform and Hardware Security, Security Composition for Automotive System Of Systems, respectively.
- Overview of German-Japanese research collaboration

